The essence of cybersecurity is not just in preparing for attacks but also in testing the effectiveness of these preparations. As a cyber security professional you’re well aware that understanding and practicing incident response can make a profound difference when cyber-attacks occur. The aim of the exercise is to equip you with the most comprehensive insights and strategies for conducting Incident Response Testing and Exercises. Leveraging information from various sources, including NIST SP 800-61, PCI DSS, and insights from the field, we’ll examine the anatomy of an effective incident response exercise, its phases, and the tools and best practices that can optimize it.
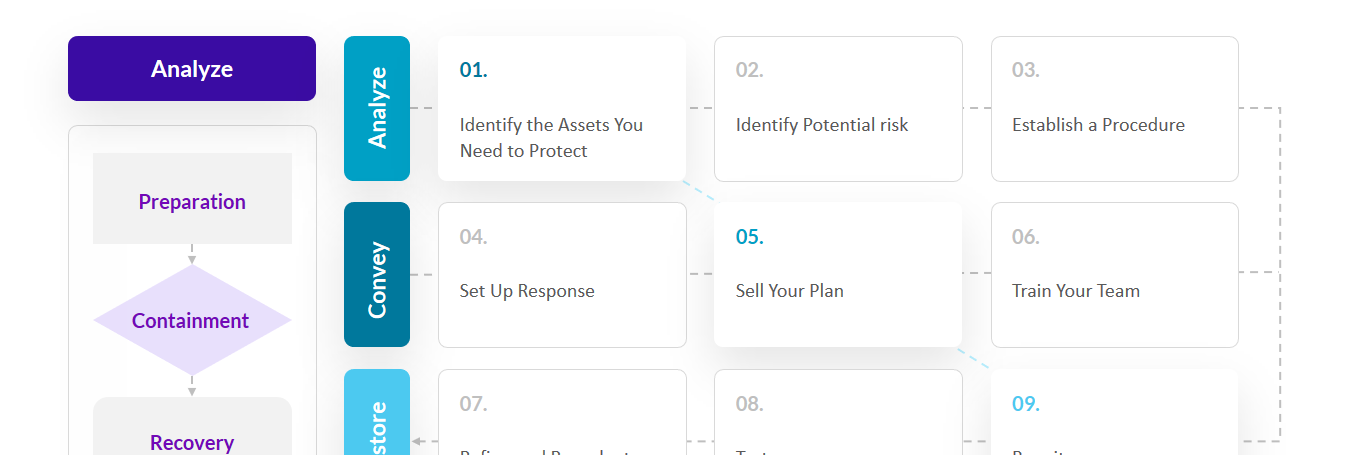
Understanding the Phases of Incident Response
1. Preparation and Planning
- Assign Roles and Responsibilities: Clearly define who does what during a cyber incident.
- Process Design: Establish an incident management flow, including a well-defined chain-of-command.
- Escalation Plan: Create procedures for escalating high-risk, high-priority incidents.
- Asset Identification: Prioritize the most critical assets in your IT infrastructure.Testing Strategy: Conduct tabletop exercises to simulate the identification and classification of an incident, focusing on roles, communication flows, and decision-making processes.
2. Threat Detection
- Classify Threats: Develop mechanisms for threat classification based on risk level, type, and origin.Testing Strategy: Use threat emulation or simulation tools to generate incidents for the team to detect. Validate the efficiency and effectiveness of your threat detection systems.
3. Threat Containment
- Isolation and Hard Drive Wiping: Utilize methods to contain the threat to prevent it from spreading across the network.Testing Strategy: Run penetration tests simulating advanced threats that require containment procedures. Check if they can be successfully contained and identify any gaps.
4. Threat Eradication
- Asset Removal and Patching: Once contained, eradicate the threat completely from the environment.Testing Strategy: Post-containment, simulate an incident scenario where the threat reappears and test eradication measures.
5. System Recovery
- Restoration: Bring affected systems back to normal operational status.Testing Strategy: Monitor system behavior post-recovery to detect any abnormal behavior.
6. Testing and Follow-Up
- Ongoing Testing: Ensure the effectiveness of your incident response plan with regular testing and updates.Testing Strategy: Periodically review and test your incident response protocols for continuous improvement.
NIST Recommendations for Incident Response Testing
- Communication: Test all communication protocols and tools.
- Analysis Tools: Ensure forensic and data analysis tools are up-to-date and functional.
- Log Retention: Evaluate your log retention policies.
Testing Resilience Against Common Attack Vectors
Run specific tests against common attack vectors like:
- Web application threats
- Email threats
- Impersonation threats
Validation of Incident Analysis Tools and Processes
- System Profiling: Validate the functionality of tools that help establish normal behavioral profiles for your IT assets.
- Log Retention: Check if logs are being effectively retained and are accessible.
Compliance Testing
Ensure your incident response plan meets regulatory requirements such as PCI DSS, especially Requirement 12 which specifically deals with incident management controls.
Dynamic Testing Methods
Tabletop Testing
Run scenario-based exercises that challenge your team’s decision-making and adaptability skills.
Penetration Testing
Conduct ethical hacking tests to identify vulnerabilities and evaluate the effectiveness of your incident response strategy.
Optimization of Incident Response Testing
- Updated Network Diagrams: Keep an up-to-date network topology to understand attack vectors.
- Automation: Use orchestration tools to automate manual processes where possible.
- Classification of Processes: Streamline identification of assets and operations at risk.
Conclusion
An effective incident response program isn’t a one-off project but an ongoing cycle of testing, learning, and adapting. The effectiveness of your incident response program depends on how realistically and comprehensively you can test it. Considering you are looking into developing a perfectly executable ACSC Essential 8 program implementation design, integrating these exhaustive incident response testing protocols can contribute significantly to achieving that goal.
Feel free to share your expertise or ask further questions.