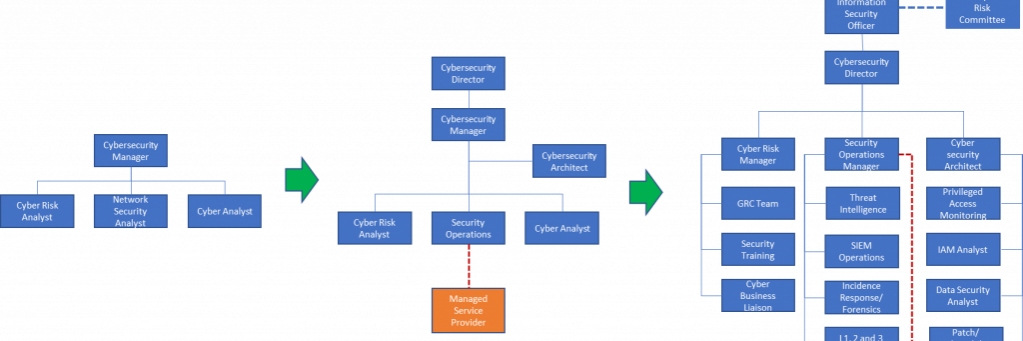
I was recently asked for an example of a well-structured organizational chart segment that focused on delivery cyber security effectively. Of course, this might vary based on the size, industry, and specific needs of the organization. Here’s some of what we came up with. What do you think?
Cyber Security Organizational Chart
1. Board of Directors
- Sub-committee for Cyber Security & Risk Management: Oversees and ensures alignment of cyber security strategy with business objectives.
2. Chief Executive Officer (CEO)
- Responsible for overall leadership and strategy.
3. Chief Information Security Officer (CISO)
- Direct Reports:
- Deputy CISO
- Governance, Risk & Compliance Manager
- Policy & Compliance Analysts
- Risk Assessment Specialists
- Security Operations Center (SOC) Manager
- Incident Response Team
- Threat Intelligence Analysts
- Identity & Access Management (IAM) Manager
- IAM Analysts
- Application Security Manager
- Application Security Analysts
- Infrastructure Security Manager
- Network Security Specialists
- Security Awareness & Training Manager
- Security Training Coordinators
- Data Protection & Privacy Officer
- Data Privacy Specialists
- Vendor & Third-Party Risk Manager
- Supplier Security Analysts
- Virtual Chief Information Security Officers (vCISO) – For Subsidiaries or Special Projects
4. Other Key Stakeholders
- Chief Information Officer (CIO)
- Chief Technology Officer (CTO)
- Chief Compliance Officer (CCO)
- Chief Data Officer (CDO)
- Legal Counsel
- Human Resources (HR)
- Business Unit Leaders
Conclusion
This organizational chart represents a sample comprehensive approach to cybersecurity within a large Australian enterprise. It emphasizes not just technical and operational aspects but also governance, risk management, compliance, and awareness. Collaboration and clear lines of reporting are vital, ensuring efficient communication between various stakeholders.
However, it’s essential to note that this chart should be tailored according to the specific needs, size, industry regulations, and risk profile of your organization. Engaging with stakeholders and possibly consulting with external experts may provide further insights into refining this structure to best suit your particular environment. Your CISO’s experience in building cyber uplift and remediation programs will undoubtedly be invaluable in crafting the perfect organizational structure for your context.